The Rise of SNMP Reflection Attacks
A few months ago we all saw the dramatic boom in NTP reflection attacks. These attacks exceeded DNS reflection that was so common before it. At the time I was personally experiencing consistent 10 to 40+ Gbps attacks. After a while they started to die down in frequency and volume. I still see many NTP reflection attacks, but in the last week I observed a large influx of SNMP based reflection attacks. It’s not the first time I’ve seen SNMP reflection in the wild, I see a few SNMP attacks every couple of months. Personally I’ve expected SNMP attacks to increase due to the large payloads generated by poorly secured SNMP daemons.
What is a reflection attack?
A reflection attack, sometimes called a DRDoS attack, is an amplified attack. The attacker starts with a small set of compromised computers, lets say 20 systems with 10Mbps connections. He has a total attack power of up to 200Mbps. That’s fine to take down a sloppy host with no protection. However it will be a challenge to impact a well designed network and a well managed server with a simple Transport/Network Layer (OSI Layer 3/4) distributed attack of such small size.
The attacker could target the Application Layer (OSI Layer 7) by crafting an attack against a service that demands many system resources on the remote network. This is a much more complex task, viable vectors could be firewalled. Most attackers must resort to a bigger Layer 3/4 attack. But how can you go bigger with just 20x 10mbps systems? Compromise more servers and grow your botnet? That’s fine a month from now, but they want to attack someone today. Paying someone else to do it will require money.
This is where reflection/amplification comes in. Attackers will scan and find recursive DNS servers, public NTP servers, public SNMP servers, etc… What all these services have in common, is their use of a certain protocol. A reflection attack exploits the stateless nature of User Datagram Protocol (UDP) and a remote server’s (ex. DNS/NTP/SNMP) willingness to reply to a spoofed source IP. Unlike Transmission Control Protocol (TCP) which is a stateful protocol requiring a handshake to establish communication, UDP requires no handshake.
A remote server using UDP will accept a packet and determine what to do with that packet. The attacker will forge a packet with a spoofed source IP address. They will use their victim’s IP address. The packet will also contain an instruction for the remote server. The remote server will accept this packet and respond back with the result of the instruction. However since UDP is stateless the remote server will accept the forged packet’s spoofed IP address and send data back to that address. The victim’s address!
How does this help the attacker? Why is this better than just spamming the victim yourself?
What the attacker will do is scan the internet for services like DNS/NTP/SNMP that will accept forged packets and reply back to the spoofed source. Lets say the attacker is targeting NTP and finds 500 such NTP servers. Let’s assume each server has 100Mbps of connectivity. Wow, that’s a potential attack of 50Gbps! Great, but how do you amplify the attack? How do you make a big attack with your 200Mbps botnet?
The attacker can exploit the difference in data required to initiate a response and the size of the response. He can send a tiny, 60 byte request packet to each of the 500 NTP servers. These servers will hit back with say a 2,600 byte output split in two packets (MTU limit) to the spoofed ip in the forged packet. As a rule DNS will return a fair amount of bytes, NTP will return even more, but SNMP can potentially return a HUGE amount of data. It all depends on the remote server you’re exploiting and how you craft your attack.
So how big will these attacks really get?
Let’s say the attacker sends 60 bytes to 500 hosts. That will require 0.23 megabits to complete. Now lets assume the responses from our ficticious NTP servers are all 2,600 bytes. That means for your 0.23 megabits, you got back 9.92 megabits, or rather your victim did!
With your 200Mbps botnet you could theoretically send out over 860 requests per second to all 500 servers. Your victim would get slammed with over 8.3Gbps!
That’s an amplification factor of over 41x and enough to be a challenge to MANY networks. Only well equipped networks with good sysadmins and netadmins can handle these attacks. If you find servers that respond with larger output, and tune your requests, you could see NTP resulting in over 200x amplification factors.
So what’s the big deal with SNMP?
SNMP, in a well tuned attack, can result in a HUGE amount of data. You could send a 68 byte packet and get a response in excess of 30,000 bytes! If you’re clever, you could concoct an attack with an amplification factor of 600x+ and that’s a scary thought!
So far I’ve not seen such large attacks, but clearly it’s interesting to people and people are playing with SNMP when attacking others. Below is a screenshot of a small 3Gbps SNMP attack I saw tonight.
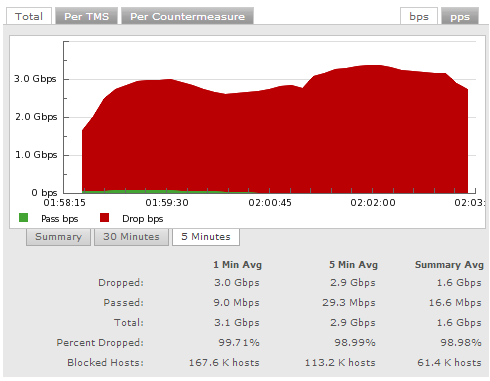
As you can tell there are well over 100,000 SNMP hosts attacking!
What can we do to stop this?
There are four things network admins and system admins should be doing.
1. Admins should follow BCP38 to prevent spoofing from their networks. If all networks follow this BCP spoofing and the reflection attacks will stop. BCP38 Documentation
2. Everyone should be securing their NTP, DNS and SNMP services. NTP should be firewalled off. I doubt 99% of you need your NTP server to be public. Are you in the business of providing time services to the whole world? Really? Just firewall it and allow only hosts under your control to talk to it. DNS recursion? Why are you doing it and making it public? Trying to be the next 4.2.2.2 (Level 3) or 8.8.8.8 (Google)? Stop it! SNMP is the same, firewall it off, use good community strings. No reason why you’d want someone peeking into your network devices with SNMP.
3. Scan your network. Find all those pesky services that should be firewalled or otherwise secured. Create a weekly report and check that it comes back empty every time.
4. Everyone should be disabling unnecessary services. Do you still have a DNS server from 2006 that you haven’t used in 8 years? Why is it online? Do you have legacy devices running CHARGEN? Why?

